Demystifying FedRAMP - Part 3 - Is system documentation included in the system boundary? What classification should be placed on our system security plan (SSP)?
Note: This is part 3 of a multi-part series. See the links below for other topics in the series.
Today we will address questions around handling and classification of the FedRAMP System Security Plan (SSP) and other documents that are included in the FedRAMP Package. This will be closely related to the next topic regarding the protection of this data.
Regarding classification, our team noted a change in the classification label across all FedRAMP package templates when the latest versions arrived in June of 2016. Previously the templates had a suggested label of "Company Sensitive and Proprietary for Authorized Use Only." The new label was "Controlled Unclassified Information." The figure below shows how the front page and the classification of the template changed from the 2014 to the 2016 version.
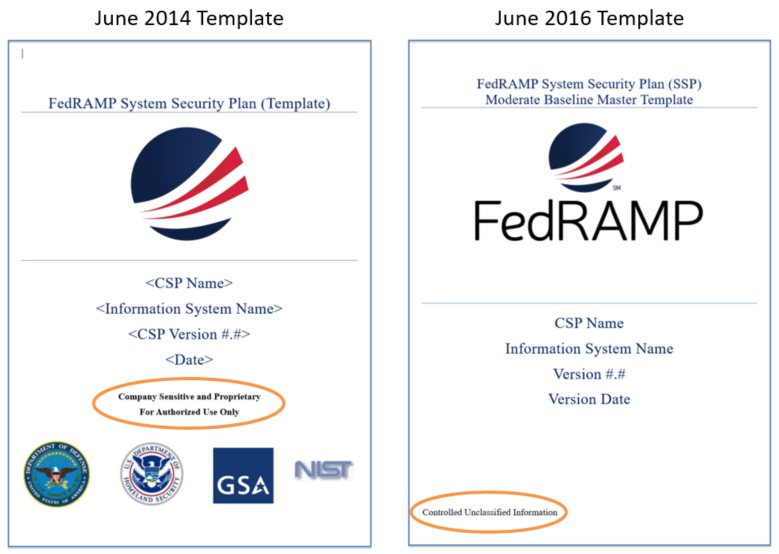
Additionally, there was a note regarding this change in the revision block for the FedRAMP templates, indicating that the change was purposeful.
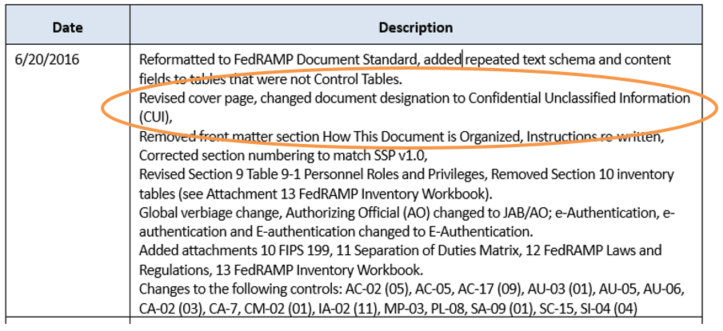
We had a strong suspicion that this modification was due to the standardization on the Controlled Unclassified Information (CUI) designation that has been ongoing in the Federal government since 2008. But we still thought it would be wise to follow-up with the FedRAMP PMO on the change to determine if the classification was a suggestion, or if it was required.
Their response:
FedRAMP is a program under GSA and is applying the CUI markings in accordance with the Government standard for protection of unclassified information. As such, the markings in the templates are required.
Information regarding the application of CUI markings can be found at https://www.archives.gov/cui/registry#categories. Relative to information systems vulnerability information, the site states,
“Related to information that if not protected, could result in adverse effects to information systems. Information system means a discrete set of information resources organized for the collection, processing, maintenance, use, sharing, dissemination, or disposition of information.”
CUI may also apply to FedRAMP documentation fitting the category of proprietary business information, where the site states,
“Material and information relating to, or associated with, a company's products, business, or activities, including but not limited to financial information; data or statements; trade secrets; product research and development; existing and future product designs and performance specifications.”
Emphasis mine. These classification labels were added across all associated document templates. From this, it is clear that FedRAMP wants cloud service providers (CSPs) to protect system documentation as controlled unclassified information (CUI), including the system security plan and the system security package. This brings into scope NIST 800-171, which is the Federal government's standard for protecting CUI in non-federal systems, which we will cover in the next topic in the series.
Also, because system documentation is categorized as a configuration item (CI) as suggested by guidance in NIST 800-128, we consider it to be best practice to include system documentation in the system boundary under configuration control. The excerpt from page 32 of NIST-128 is shown below.
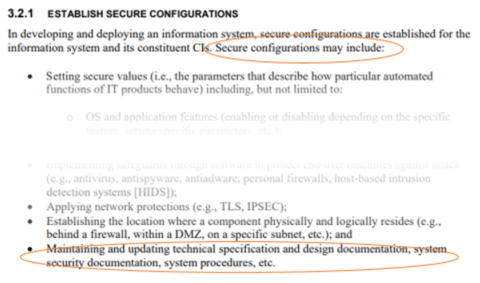
So, does that mean that the system security plan (SSP) and FedRAMP documentation must stay in your system and cannot leave the boundary? Well, no… it merely means that you should manage changes and protect system documentation according to its security categorization... And this leads us to the next topic in our series “Who should be allowed to work on the system or access the SSP documentation? What about non-US Persons / non-US Citizens?”
Use the links below for other topics in this series.
- Part 1 - Is an NDA with FedRAMP needed to protect my company’s trade secrets?
- Part 2 - If I follow FedRAMP requirements and get a pATO, my cloud service will be well designed and attractive to Federal Agencies, right?
- Part 3 - Is system documentation included in the system boundary? What classification should be placed on our system security plan and overall package?
- Part 4 – Who is allowed to work on the system or access the SSP documentation? What about non-US Persons / non-US Citizens?
- Part 5 - What is required to accomplish continuous monitoring, and how can we prepare?
- Part 6 - How should I classify my system?